EITCA/IS Information Technologies Security Academy

EITCA/IS Information Technologies Security Academy is an EU based, internationally recognized standard of expertise attestation encompassing knowledge and practical skills in the field of cybersecurity.
The curriculum of the EITCA/IS Information Technologies Security Academy covers professional competencies in the areas of computational complexity, classical cryptography (including both private-key symmetric cryptography and public-key asymmetric cryptography), quantum cryptography (with emphasis on QKD, quantum key distribution), quantum information and quantum computation introduction (including notion of quantum circuits, quantum gates and quantum algorithmics with emphasis on practical algorithms such as Shor factorization or discrete log finding algorithms), computer networking (including theoretical OSI model), computer systems security (covering fundamentals and advanced practical topics, including mobile devices security), network servers administration (including Microsoft Windows and Linux), web applications security and web application penetration testing (including several practical pentesting techniques).
Obtaining the EITCA/IS Information Technologies Security Academy Certification attests acquiring skills and passing final exams of all the substituent European IT Certification (EITC) programmes constituting the full curriculum of the EITCA/IS Information Technologies Security Academy (also available separately as single EITC certifications).
Protection of computer systems and networks from information disclosure, theft of or damage to hardware, software, or to the processed data, as well as disruption or misdirection of communication or electronic services provided, is generally referred to as computer security, cybersecurity, or information technology(ies) security (IT security). Due to the growing reliance of world functioning on computer systems (including social and economic planes) and particularlyon the Internet communication, as well as wireless networks standards such as Bluetooth and Wi-Fi, along with growing dissemination of so called smart devices such as smartphones, smart TVs, and various other devices that make up the Internet of things, the field of IT security (cybersecurity) is becoming increasingly important. Due to its complexity in terms of social, economical and political implications (including those of national security), as well as complexity in terms of technologies involved, cybersecurity is one of the most critical concerns in the modern world. It is also one of the most prestigous IT specialization characterized by an ever increasing demand for highly trained specialists with their skills properly developed and attested, that may give a lot of satisfaction, open fast career tracks development, allow for involvement in important projects (including strategic national security projects) and enable paths for further narrow specializations in different domains of this field. The job of cybersecurity expert (or a cybersecurity officer in a private or public organization) is a demanding one but also rewarding and very responsible. Expertise in both theoretical foundations and practical aspects of modern cybersecurity guarantees not only a very interesting and cutting edge information technologies related futuristic job, but also considerably higher salaries and fast career development tracks due to significant deficiencies of certified cybersecurity professionals and widespread competencies gaps related to both theoretical knowledge and practical skills in information technologies security. IT security paradigms have evolved rapidly in recent years. This is not surprising as securing of information technologies is closely related to the architectures of systems that store and process information. Dissemination of Internet services, particularly in ecommerce, have driven already dominating share of economy into virtual data. It is no secret that currently most of the economic transactions globally goes through electronic channels, which of course require proper levels of security.
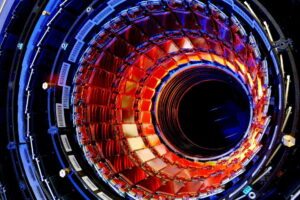
To understand cybersecurity and to be able to develop further theoretical and practical skills in this field one should first understand basics of computation theory (computation complexity) as well as basics of cryptography. The first field defines foundations for computer science and the second one (cryptography) defines foundations of secure communication. Cryptography in itself was present in our civilization from ancient times to provide means to protect secrecy of communication, and in more general terms to provide its authenticity and integrity. Modern classical cryptography has been divided into information-theoretic (unbreakable) symmetric (private-key) cryptography (based on the one-time pad cipher, however unable to solve the problem of the key distribution through communication channels) and conditionally secure asymmetric (public-key) cryptography (initially solving the problem of the key distribution and later evolving into cryptosystems working with so called public keys that were to be used for data encryption and were bound in asymmetric relations of computational complexity terms with private keys, hard to compute from their corresponding public keys, that could be used to decrypt data). The public-key cryptography as practially surpassing application potentials of private-key cryptography has dominated the Internet and currently is a main standard in securing Internet private communication and ecommerce. In 1994 however there has been a major breakthrough, which has shown that quantum algorithms can break most common public-key cryptosystems (e.g. the RSA cipher based on the factorization problem). On the other hand quantum information has provided a completely new paradigm for cryptography, namely the quantum key distribution (QKD) protocol, that allows to practically implement unbreakable (information-theoretic) secure cryptosystems for the first time in the history (not even breakable with any quantum algorithm). An expertise in these areas of modern developments of cybersecurity lays foundations for practical skills that can be applied to mitigate cyber threats to networks, computer systems (including servers but also personal computers and mobile devices) and various applications (most importantly web applications). All these fields are covered by the EITCA/IS Information Technologies Security Academy, integrating expertise in both theoretical and practical areas of cybersecurity, complementing skills with penetration testing expertise (including practical web pentesting techniques).
Since the advent of the Internet and the digital change that has occurred in recent years, the concept of cybersecurity has become a common topic in both our professional and personal life. For the last 50 years of technological advancement, cybersecurity and cyber threats have followed the development of computer systems and networks. Until the invention of the Internet in the 1970s and 1980s, computer systems and networks security was primarily relegated to academia, where, with growing connectivity, computer viruses and network intrusions began to take off. The 2000s saw the institutionalization of cyber risks and cybersecurity, following the rise of viruses in the 1990s. Large-scale attacks and government legislation began to emerge in the 2010s. Willis Ware’s April 1967 session at the Spring Joint Computer Conference, as well as the subsequent publication of the Ware Report, were watershed milestones in the history of computer security.
The so-called CIA trinity of Confidentiality, Integrity, and Availability was established in a 1977 NIST publication as a clear and easy approach to explain essential security requirements. Many more comprehensive frameworks have since been presented, and they are still evolving. However, there were no serious computer risks in the 1970s and 1980s since computers and the internet were still at early stage of development with relatively low connectivity, and security threats were easily detected in limited domains of operations. Malicious insiders who got unauthorized access to critical documents and files were the most common source of danger. They did not employ malware or network breaches for financial advantage in the early years, despite the fact that they existed. Established computer companies, such as IBM, began developing commercial access control systems and computer security software in the second half of the 1970s.
The era of malicious computer programs (worms or viruses if they had programmed properties of self replication and contagous operations, spreading themsselves in computer systems through networks and other means) began in 1971 with so called Creeper. Creeper was a BBN-developed experimental computer program considered be the first computer worm. Reaper, the first anti-virus software, was developed in 1972. It was built in order to migrate across the ARPANET and eliminate the Creeper worm. A group of German hackers committed the first documented act of cyber espionage between September 1986 and June 1987. The gang hacked into the networks of American defense firms, universities, and military bases, selling the data to the Soviet KGB. Markus Hess, the group’s leader, was captured on June 29, 1987. On February 15, 1990, he was found guilty of espionage (together with two co-conspirators). Morris worm, one of the first computer worms, was disseminated via the Internet in 1988. It received a lot of coverage in the mainstream media. Soon after the National Center for Supercomputing Applications (NCSA) released Mosaic 1.0, the first web browser, in 1993, Netscape began creating the SSL protocol. In 1994, Netscape had SSL version 1.0 ready, but it was never released to the public due to a number of major security flaws. Replay attacks and a vulnerability that allowed hackers to change unencrypted messages delivered by users were among the flaws discovered. Netscape, on the other hand, released Version 2.0 in February 1995.
In the US, the National Security Agency (NSA) is in charge of protecting American information networks as well as gathering foreign intelligence. These two responsibilities are incompatible. As a defensive measure, reviewing software, finding security problems, and taking efforts to repair the flaws are all part of protecting information systems. Exploiting security holes to obtain information is part of gathering intelligence, which is a hostile action. When security weaknesses are fixed, they are no longer exploitable by the NSA. The NSA examines widely used software in order to identify security holes, which it then uses to launch offensive attacks against US competitors. The agency rarely takes defensive action, such as disclosing security issues to software developers so that they can be fixed. For a time, the offensive strategy worked, but other countries, such as Russia, Iran, North Korea, and China, gradually developed their own offensive capacity, which they now utilize against the US. NSA contractors developed and sold simple one-click solutions and assault tools to US agencies and allies, but the tools eventually found their way into the hands of foreign adversaries, which have been able to study them and develop their versions. The NSA’s own hacking capabilities were hacked in 2016, and Russia and North Korea have exploited them. Adversaries eager to compete in cyberwarfare have hired NSA workers and contractors at exorbitant wages. For example, in 2007, the US and Israel began attacking and damaging equipment used in Iran to refine nuclear materials by exploiting security holes in the Microsoft Windows operating system. Iran retaliated by massively investing in its own cyberwarfare capability, which it immediately began employing against the US. It should be noted that currently the cybersecurity field is widely treated as a strategic national security field and means of possible future warfare.
The EITCA/IS Certificate provides a comprehensive attestation of professional competencies in the area of IT security (cybersecurity) ranging from foundations to advanced theoretical knowledge, as well as including practical skills in classical as well as quantum cryptosystems, secure computer networking, computer systems security (including security of mobile devices) servers security and applications security (including web applications security and penetration testing).
EITCA/IS Information Technologies Security Academy is an advanced training and certification programme with the referenced high-quality open-access extensive didactic content organized in a step-by-step didactic process, selected to adequately address the defined curriculum, educationally equivalent to international post-graduate studies in cybersecurity combined with the industry-level cybersecurity digital training, and surpassing standardized training offers in various fields of applicable IT security available on the market. The content of the EITCA Academy Certification programme is specified and standardized by the European Information Technologies Certification Institute EITCI in Brussels. This programme is successively updated on an ongoing basis due to advancements in cybersecurity field in accordance with the guidelines of the EITCI Institute and is subject to periodic accreditations.
The EITCA/IS Information Technologies Security Academy programme comprises relevant constituent European IT Certification EITC programmes. The list of EITC Certifications included in the complete EITCA/IS Information Technologies Security Academy programme, in accordance with the specifications of the European Information Technologies Certification Institute EITCI, is presented below. You can click on respective EITC programmes listed in a recommended order to individually enrol for each EITC programme (alternatively to enrolling for the complete EITCA/IS Information Technologies Security Academy programme above) in order proceed with their individual curriculums, preparing for corresponding EITC examinations. Passing all examinations for all of the substituent EITC programmes results with completion of the EITCA/IS Information Technologies Security Academy programme and with granting of the corresponding EITCA Academy Certification (supplemented by all its substituent EITC Certifications). After passing each individual EITC examination you will be also issued the corresponding EITC Certificate, before completing the whole EITCA Academy.
EITCA/IS Information Technologies Security Academy constituent EITC programmes